Securely Connect Remote IoT P2P SSH Download Android: The Ultimate Guide
Hey there, tech enthusiasts! If you're looking to securely connect remote IoT devices using P2P SSH on Android, you're in the right place. In today's digital age, securing your IoT devices is more important than ever. As hackers get smarter, so should we. This guide will walk you through everything you need to know about safely connecting your remote IoT gadgets via P2P SSH on Android. Let’s dive in and make sure your data stays safe while you enjoy the convenience of modern tech.
Nowadays, IoT devices are everywhere—from smart fridges to security cameras. But with great convenience comes great responsibility. You’ve gotta protect your devices from potential threats. That’s where P2P SSH comes into play. It’s like giving your IoT devices a digital fortress to keep unwanted visitors out.
In this article, we’ll cover everything from the basics of P2P SSH to advanced tips for securing your IoT devices on Android. Whether you're a tech newbie or a seasoned pro, this guide has got you covered. So grab your favorite drink, sit back, and let’s explore how to keep your IoT world safe and secure.
Read also:Funkitaun Cartel The Rise And Fall Of A Modernday Empire
Understanding the Basics of IoT Security
Before we dive into the nitty-gritty of securely connecting remote IoT devices, let’s talk about the basics of IoT security. IoT stands for Internet of Things, which refers to any device connected to the internet. From your smart thermostat to your fitness tracker, these devices are designed to make life easier. But with that convenience comes the risk of cyber threats.
IoT security is all about protecting these devices from unauthorized access. Think of it like locking your front door to keep burglars out. In the digital world, securing your IoT devices means using strong passwords, encryption, and secure connections like P2P SSH.
Here’s why IoT security matters:
- Protects your personal data from hackers.
- Prevents unauthorized access to your devices.
- Keeps your network safe from malware and viruses.
What is P2P SSH and Why Should You Care?
P2P SSH, or Peer-to-Peer Secure Shell, is a method of securely connecting two devices over the internet. It’s like creating a private tunnel between your devices, so no one else can eavesdrop on your data. This is especially important when dealing with IoT devices, as they often transmit sensitive information.
Here’s how P2P SSH works:
- It establishes a direct connection between two devices.
- It encrypts all data transmitted between the devices.
- It authenticates both devices to ensure secure communication.
By using P2P SSH, you can rest assured that your IoT devices are communicating securely. This is crucial for protecting your data and maintaining the integrity of your network.
Read also:Vereena Motorcycle Accident News The Inside Story You Need To Know
Why Android is the Perfect Platform for IoT
Android is one of the most popular operating systems in the world, and for good reason. It’s flexible, customizable, and compatible with a wide range of devices. When it comes to IoT, Android offers several advantages that make it the perfect platform for secure connections.
Firstly, Android has a large developer community, which means there are tons of apps and tools available for IoT enthusiasts. Secondly, Android devices are highly customizable, allowing you to tailor your setup to meet your specific needs. Lastly, Android offers robust security features, such as app permissions and encryption, to keep your data safe.
Here are some reasons why Android is great for IoT:
- Wide range of compatible devices.
- Large developer community.
- Customizable settings.
- Robust security features.
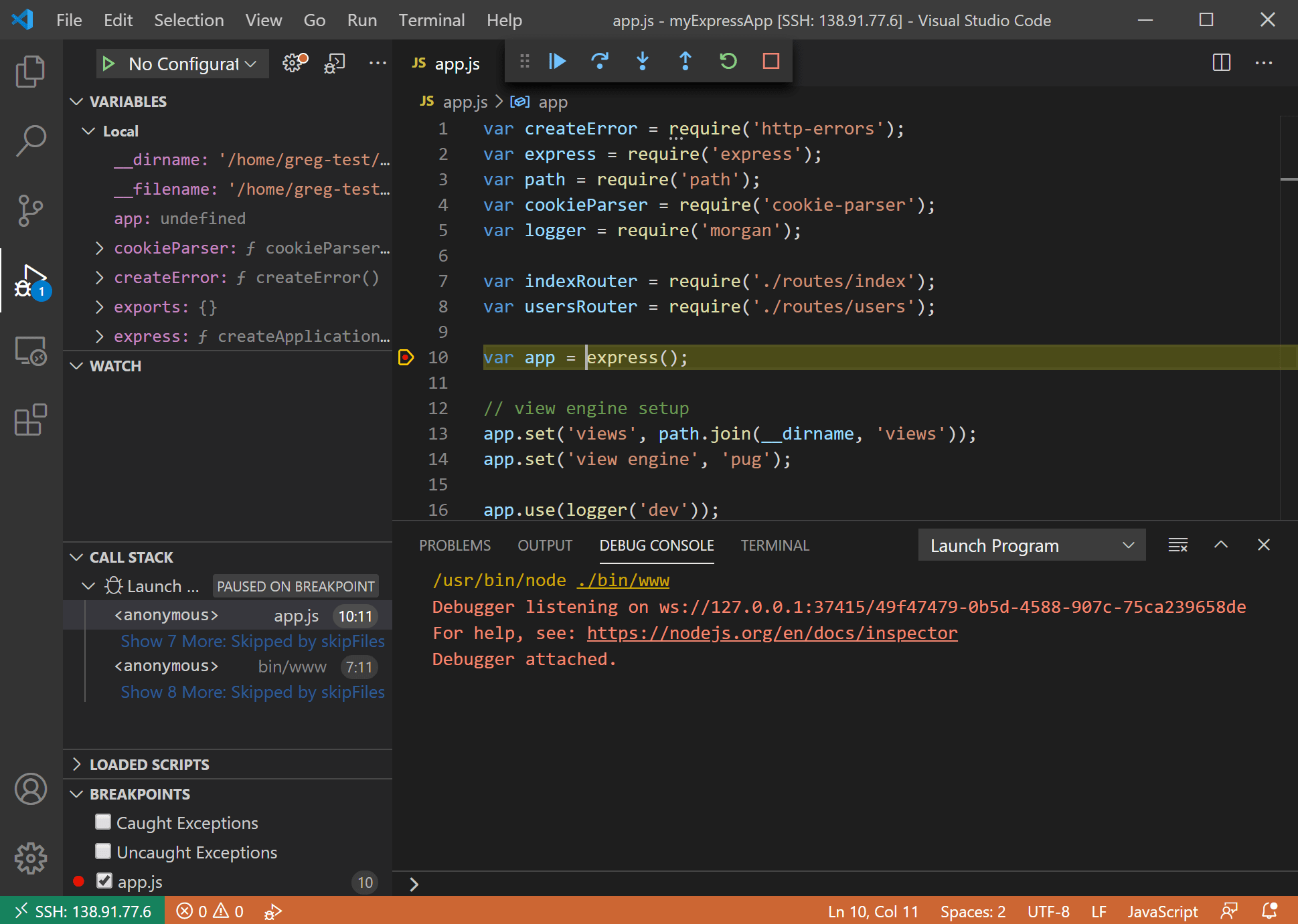
Setting Up P2P SSH on Android
Setting up P2P SSH on Android is easier than you might think. With the right tools and a little know-how, you can have your IoT devices securely connected in no time. Here’s a step-by-step guide to help you get started:
Step 1: Download an SSH client app from the Google Play Store. Some popular options include JuiceSSH and Termux.
Step 2: Install the app and open it on your Android device.
Step 3: Enter the IP address and port number of your IoT device.
Step 4: Enter your login credentials, including username and password.
Step 5: Connect to your IoT device using the SSH client.
That’s it! You’re now securely connected to your IoT device via P2P SSH on Android.
Securing Your IoT Devices with P2P SSH
Now that you know how to set up P2P SSH on Android, let’s talk about securing your IoT devices. Security should always be a top priority when dealing with IoT devices, as they often contain sensitive information. Here are some tips to help you keep your devices safe:
- Use strong, unique passwords for each device.
- Enable two-factor authentication whenever possible.
- Keep your firmware and software up to date.
- Use encryption to protect your data.
- Limit access to your devices to trusted users only.
By following these tips, you can significantly reduce the risk of cyber attacks and keep your IoT devices secure.
Common Mistakes to Avoid When Using P2P SSH
Even with the best intentions, mistakes can happen. Here are some common mistakes to avoid when using P2P SSH:
- Using weak passwords or reusing passwords across devices.
- Not enabling encryption for your connections.
- Ignoring software updates and security patches.
- Sharing your login credentials with others.
Avoiding these mistakes will help ensure that your P2P SSH connections remain secure and reliable.
Best Practices for IoT Security
When it comes to IoT security, there are several best practices you should follow to keep your devices safe. Here are some tips to help you stay ahead of the curve:
- Regularly monitor your devices for suspicious activity.
- Use a firewall to protect your network from unauthorized access.
- Limit the amount of data your devices collect and store.
- Be cautious when downloading apps or software for your IoT devices.
By following these best practices, you can create a secure environment for your IoT devices and minimize the risk of cyber threats.
Tools and Resources for IoT Security
There are several tools and resources available to help you secure your IoT devices. Here are a few you might find useful:
- Shodan: A search engine for IoT devices that can help you identify vulnerabilities.
- Wireshark: A network protocol analyzer that can help you monitor your connections.
- Nmap: A network scanning tool that can help you identify potential security risks.
These tools can provide valuable insights into your IoT setup and help you identify areas for improvement.
Real-World Applications of P2P SSH
P2P SSH isn’t just a theoretical concept; it has real-world applications that can benefit individuals and businesses alike. Here are a few examples:
- Remote monitoring of industrial equipment.
- Secure communication between smart home devices.
- Protected data transfer for healthcare devices.
By implementing P2P SSH, organizations can enhance the security of their IoT deployments and protect sensitive information.
Case Studies: How P2P SSH is Being Used Today
Let’s take a look at some real-world case studies where P2P SSH is making a difference:
Case Study 1: A manufacturing company uses P2P SSH to securely monitor their industrial equipment from remote locations. This allows them to quickly identify and address issues, reducing downtime and improving efficiency.
Case Study 2: A healthcare provider uses P2P SSH to protect the transmission of patient data between devices. This ensures compliance with regulations and maintains patient privacy.
These examples demonstrate the versatility and effectiveness of P2P SSH in various industries.
Future Trends in IoT Security
The world of IoT security is constantly evolving, and there are several trends to watch out for in the coming years. Here are a few to keep an eye on:
- Increased adoption of blockchain technology for secure data storage.
- Development of AI-driven security solutions to detect and respond to threats in real-time.
- Greater emphasis on privacy and data protection regulations.
By staying informed about these trends, you can prepare for the future of IoT security and ensure your devices remain protected.
Preparing for the Future of IoT Security
To prepare for the future of IoT security, consider the following tips:
- Invest in cutting-edge security technologies.
- Stay up to date with the latest trends and best practices.
- Engage in continuous education and training to enhance your knowledge.
By taking proactive steps, you can stay ahead of the curve and protect your IoT devices from emerging threats.
Conclusion: Securing Your IoT World
And there you have it, folks! A comprehensive guide to securely connecting remote IoT devices using P2P SSH on Android. By following the tips and best practices outlined in this article, you can create a secure environment for your IoT devices and protect your data from potential threats.
Remember, security is an ongoing process. Stay vigilant, stay informed, and don’t hesitate to reach out if you have any questions or concerns. Feel free to leave a comment below or share this article with your friends and colleagues. Together, we can make the IoT world a safer place!
Call to Action
What are you waiting for? Start securing your IoT devices today! Download the necessary apps, set up P2P SSH, and take control of your digital world. And don’t forget to check out our other articles for more tips and tricks on tech and security. Happy securing, and see you in the comments!
Article Recommendations